Get Your Free ISO 27001 Readiness Report
✅ 100% Free — No credit card requiredA 30-minute working session with our compliance team plus a written assessment of where your stack stands against ISO 27001:2022.
- Per-control Annex A gap analysis against your current setup
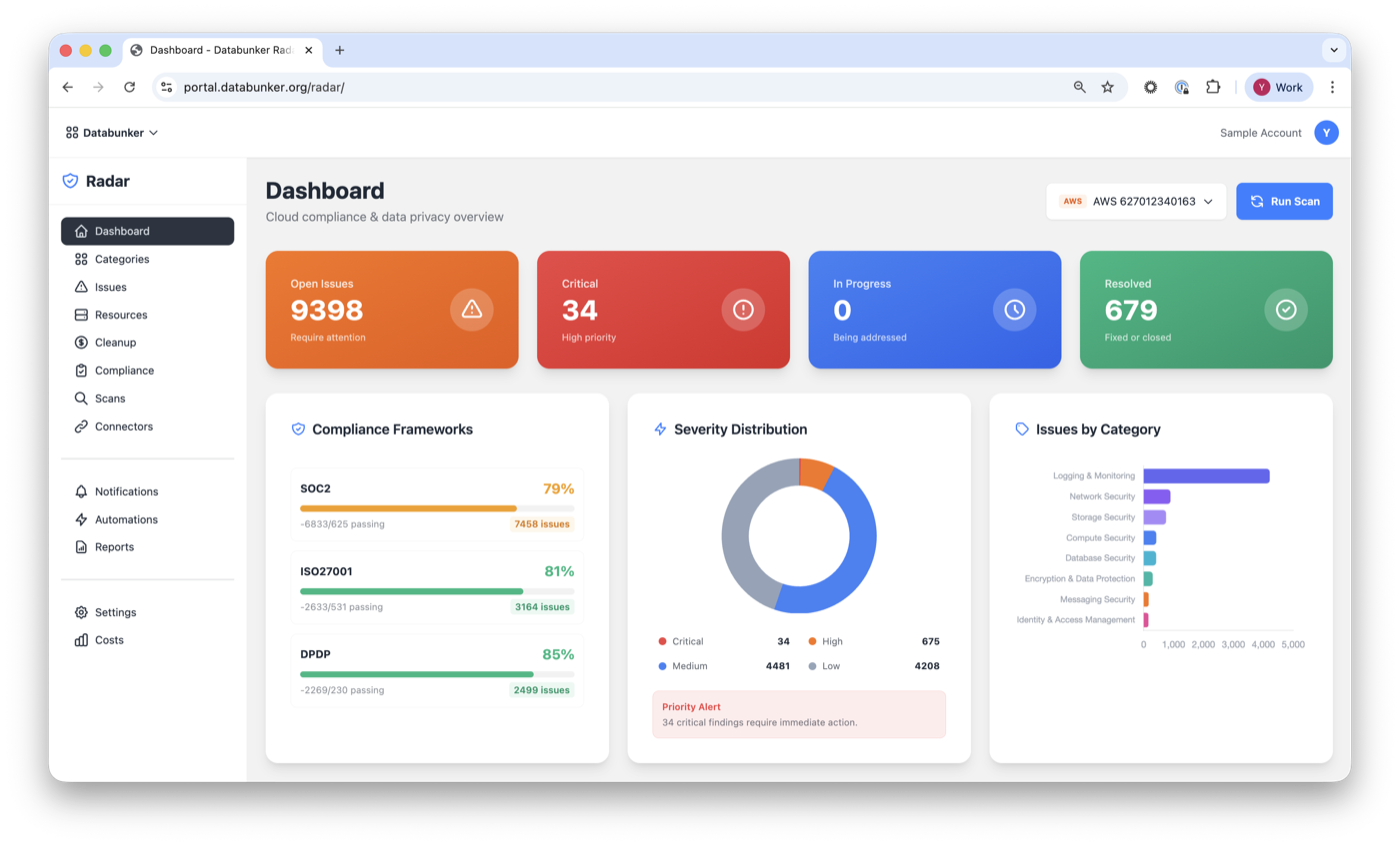
- Cloud + database compliance scan via Databunker Radar — 1,000+ checks mapped to Annex A
- Remediation roadmap — concrete next steps prioritised by certification risk
- Tool / tier recommendation across Pro / Radar / DPO
Drill into findings by Annex A control — and export an audit-ready report.
Book Your Free ISO 27001 Assessment
Tell us a bit about your stack — our compliance team will respond within 24 hours.
✓ 24-hour response · ✓ 30-minute call · ✓ No credit card required